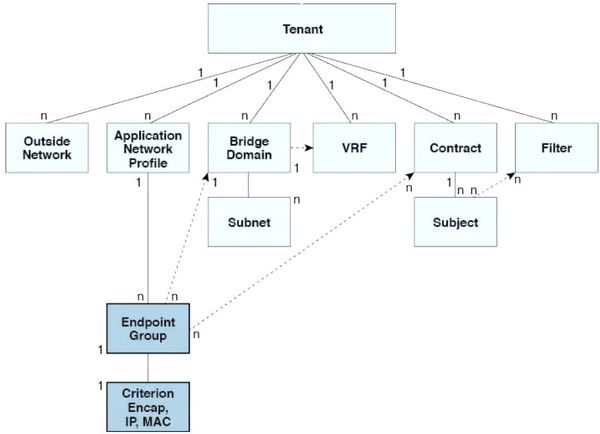
Cisco ACI – Policy Driven Architecture
Making sense of the Cisco ACI policy model

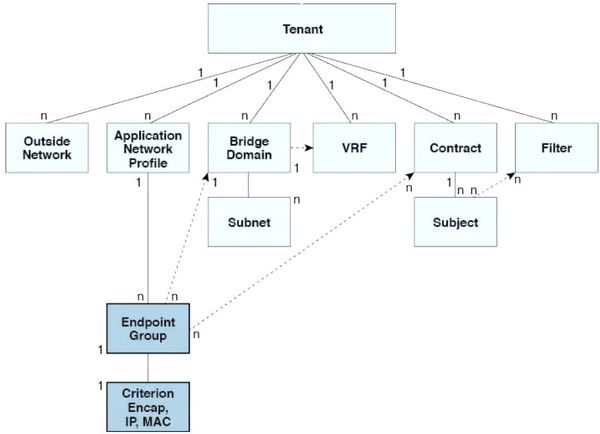
Making sense of the Cisco ACI policy model
If you work in manufacturing, energy, utilities, or critical infrastructure, the stakes of your cybersecurity are profoundly different. You are not just guarding data—you are guarding things that spin, pump, flow, and explode. The key focus is to protect the process, rather than the information itself. This is the

An Industrial Demilitarised Zone (IDMZ) firewall is a specialised security boundary that acts as a buffer between an industrial control system (ICS) network and an enterprise IT network.

Is Artificial Intelligence (AI) a net benefit to the internet? I'm seeing an increasing amount of AI-generated content on the internet and social media. Especially as media content is becoming more realistic. I don’t particularly find the created content organic or interesting. In a 2025 Study,

This is a post on research I conducted regarding the deployment of critical systems onto Software-Defined Network (SDN) environments— specifically, Cisco SDA. I've uploaded the research proposal and the research report.

I thought I would write a brief piece on Cloud 101 and an introduction to the cloud! First, we need to define what a cloud is, as described by NIST 800-145: Cloud computing provides easy, on-demand access to shared computing resources — such as networks, servers, storage, and applications

The COVID-19 pandemic reshaped how we work, accelerating the shift toward remote work. As businesses adapt, realising they can reduce office space and environmental costs, working from home is becoming a lasting trend. Work is now an activity, not a destination. To thrive in this environment, you need strategies